Introduction
The ActivityInfo Self-managed Server can be configured through the Server Settings user interface. This interface is **only ** accessible to the system administrator whose email and password were provided during the installation process.
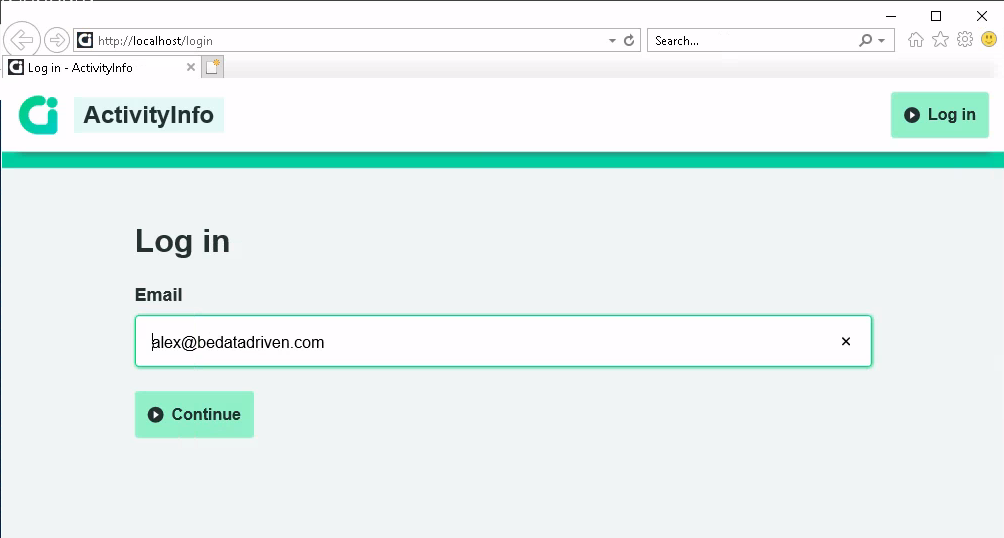
Navigate to http://localhost to login with these credentials.
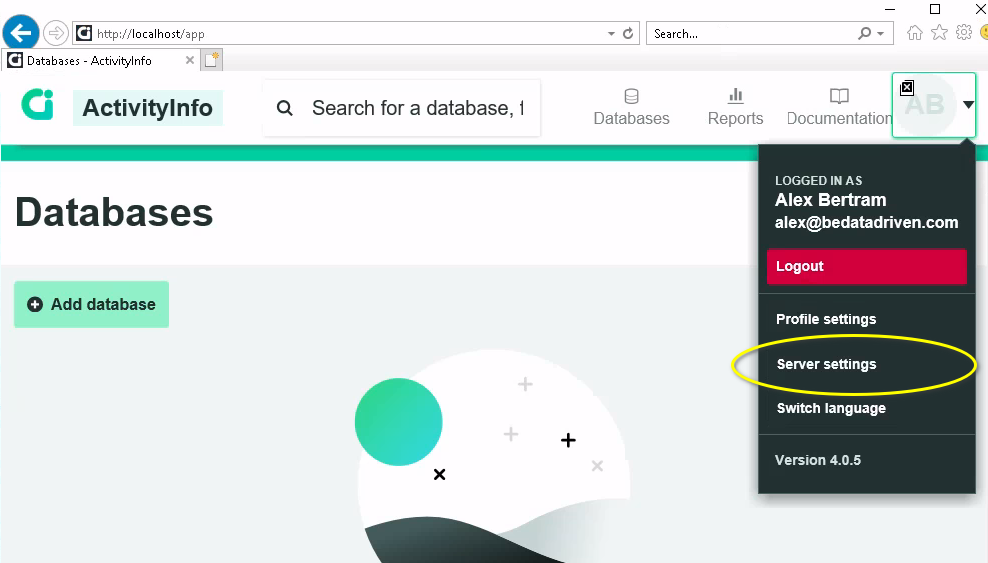
You can access the Server settings interface from the profile menu:
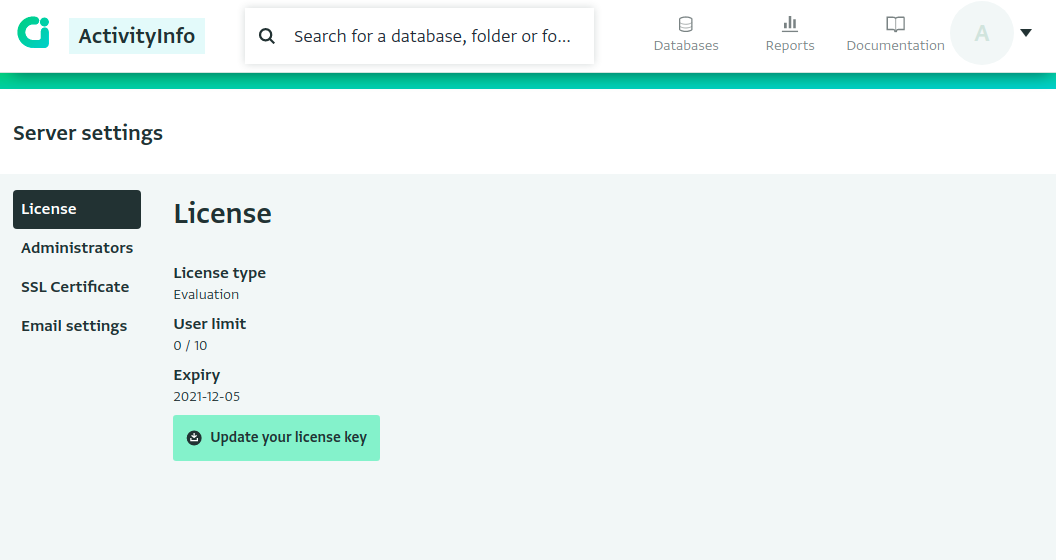
This will open the Server Settings interface:
SSL configuration
The first thing you must configure is an SSL certificate for your ActivityInfo server, which ensures an encrypted connection between the ActivityInfo Server and your users' browser.
This is not only important for security, but it is required for a number of ActivityInfo features to fully function, such as offline availability. This is because the ActivityInfo JavaScript application uses some features that are only available to JavaScript applications over secure connections.
If your ActivityInfo server will be publicly accessible over the Internet, we recommend setting up automated certificate management with Let's Encrypt.
If you are only using ActivityInfo on an internal network, you should still configure an SSL certificate, but you will need to manually manage certificates. Please see the following guides depending on your environment:
- Active Directory Certificate Services on Windows Server 2012 and later
Alternatively, you may already have a load balancer or a reverse proxy in place that provides SSL termination. In this case, you must enable HTTPS Proxy mode.
Single-sign on (SSO) configuration
Different Identity Providers (IdPs) can be configured to provide authentication for ActivityInfo users with different email domains.
For example, you can configure Azure Active Directory to provide authentication for users in your domain (e.g. alice@example.gov ) and Google Accounts to provide authentication for external parties with @gmail.com addresses.
The following Identity Providers (IdPs) are supported:
Active Directory
You can connect to Azure Active Directory (AAD) or Active Directory Federation Services (ADFS) using the OpenID Connect protocol.
Google Accounts
You can connect to Google Accounts to provide Single-Sign On (SSO) for your organization if you use Google Workspace as well as for public GMail accounts.